Azure Virtual Desktop - Prepare for Secure Boot Certificate Changes by June 2026
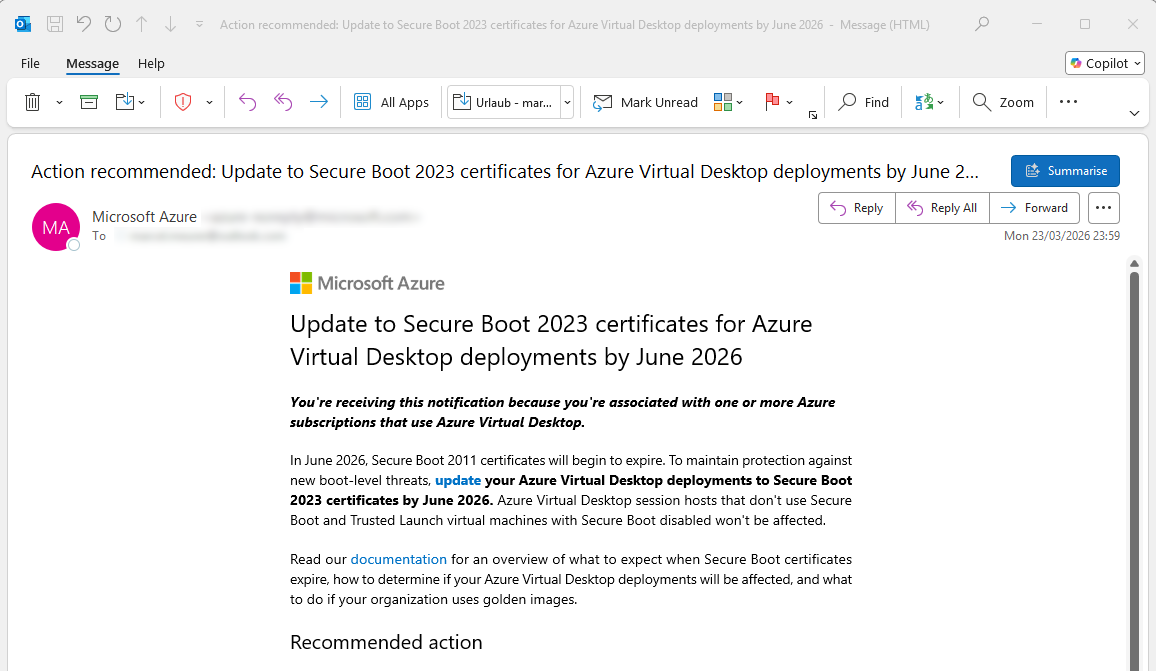
Microsoft has started notifying customers using Azure Virtual Desktop about an important upcoming change:
Secure Boot 2011 certificates will begin to expire in June 2026.
While that might sound far away, environments using older images may already require attention today.
What’s Changing?
Secure Boot plays a critical role in protecting the early boot process from tampering and low-level threats. As part of ongoing security improvements, Microsoft is transitioning from the 2011 certificates to the newer Secure Boot 2023 certificates.
Once the old certificates expire, systems that haven’t been updated may:
- Lose protection against newer boot-level threats
- Encounter boot or validation issues (depending on configuration)
Important:
Only systems with Secure Boot enabled are affected. Environments without Secure Boot or without Trusted Launch VMs do not require action.
Who Should Care?
This is especially relevant if your organization:
- Uses Azure Virtual Desktop
- Maintains custom images or golden images
- Runs long-lived VM templates
In many cases, these images were created years ago and still contain outdated Secure Boot certificates.
Microsoft’s Recommendation
Microsoft advises customers to:
- Identify affected deployments
- Update images and session hosts
- Transition to Secure Boot 2023 certificates before June 2026
Key takeaway:
If you are using older images, you should validate them now rather than later.
Simplifying the Process with Automation
To streamline this process, I created a small PowerShell script that helps:
- ✔️ Check whether an update is required
- ✔️ Apply the update if needed
Execution requirements: - Run in an elevated (Administrator) PowerShell session
- Reboot the system after applying changes
You can find the script here:
https://gist.github.com/MarcelMeurer/01db5590b2af52cc630c7bd29befaf63
Pro Tip: Integrate it in Hydra
Instead of treating this as a one-time fix, consider embedding the check/update into your image lifecycle.
For example, you can use it as a pre-configuration script when building images with Hydra (Optional.: Run a Script or Collection on the Master first).
This ensures that:
- New images are always compliant
- Manual validation steps are reduced
- Future certificate rotations become easier to handle
Final Thoughts
June 2026 may seem distant, but certificate-related changes tend to surface at the worst possible time—during deployments or recovery scenarios.
Taking a proactive approach now will:
- Reduce operational risk
- Avoid last-minute remediation efforts
- Keep your Azure Virtual Desktop environment secure and compliant
Action: check your images early, automate where possible, and stay ahead of the deadline.